Cisco Asa 5505 Keymaker
Posted : admin On 11.01.2020Installing the Chassis The ASA ships with a default configuration that includes two preconfigured networks (the Inside network and the Outside network) and an Inside interface configured for a DHCP server. Clients on the Inside network obtain a dynamic IP address from the ASA so that they can communicate with each other as well as with devices on the Internet. Step 1 Connect one end of an Ethernet cable (not provided) to Ethernet 0 on the ASA. (By default, Ethernet 0 is the Outside interface.) Connect the other end to a cable/DSL modem or gateway router (the Outside network). Step 2 Connect your devices (such as PCs, printers, and servers) with Ethernet cables to Ethernet 1 through 7.
Powering on and Verifying Interface Connectivity Step 1 Connect the power supply adaptor to the power cable. Step 2 Connect the rectangular connector of the power supply adaptor to the power connector on the rear panel of the ASA. Step 3 Connect the AC power connector of the power cable to an electrical outlet.
(The ASA does not have a power switch. Completing this step powers on the device.) Step 4 Check the Power LED on the front of the ASA; if it is solid green, the device is powered on.
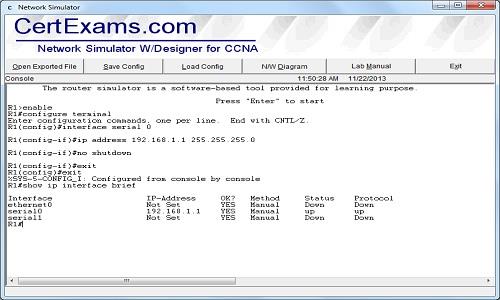
Step 5 Check your management PC to make sure it received an IP address on the 192.168.1.0/24 network using DHCP. Step 6 Check the LINK/ACT indicators to verify interface connectivity. Initial Configuration Considerations The ASA ships with a default configuration that, in most cases, is sufficient for your basic deployment. You configure the ASA by using ASDM.
Cisco Asa 5505 Keymaker

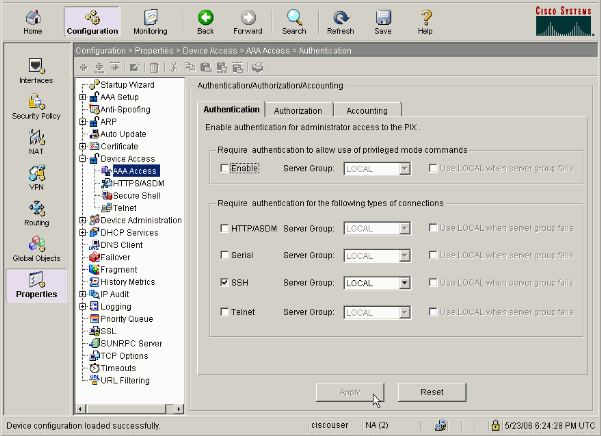
ASDM is a graphical interface that allows you to manage the ASA from any location by using a web browser. However, changing certain settings is recommended or required. For example, you should change the following settings from their defaults:. The privileged EXEC mode (enable) password that is required to administer the ASA through ASDM and the CLI. When using the ASA as a VPN endpoint (using the SSL VPN features): – The hostname, domain name, and DNS server names – Outside interface IP address to a static address – Identity certificate – WINS names when access to Windows file shares is required Use the Startup Wizard in ASDM to make these changes. (Optional) Allowing Access to Public Servers Behind the ASA The Public Server pane automatically configures the security policy to make an inside server accessible from the Internet. As a business owner, you might have internal network services, such as a web and FTP server, that need to be available to an outside user.
You can place these services on a separate network behind the ASA, called a demilitarized zone (DMZ). By placing the public servers on the DMZ, any attacks launched against the public servers do not affect your inside networks. (Optional) Running VPN Wizards You can configure VPN using the following wizards:. Site-to-Site VPN Wizard—Creates an IPsec site-to-site tunnel between two ASAs. AnyConnect VPN Wizard—Configures SSL VPN remote access for the Cisco AnyConnect VPN client.
AnyConnect provides secure SSL connections to the ASA for remote users with full VPN tunneling to corporate resources. The ASA policy can be configured to download the AnyConnect Client to remote users when they initially connect via a browser. With AnyConnect 3.0 and later, the client can run either the SSL or IPSec IKEv2 VPN protocol. Clientless SSL VPN Wizard—Configures clientless SSL VPN remote access for a browser. Clientless, browser-based SSL VPN lets users establish a secure, remote-access VPN tunnel to the ASA using a web browser.
After authentication, users access a portal page and can access specific, supported internal resources. The network administrator provides access to resources by users on a group basis.
ACLs can be applied to restrict or allow access to specific corporate resources. IPsec (IKEv1) Remote Access VPN Wizard—Configures IPsec VPN remote access for the Cisco IPsec client.
Hidden Content You'll be able to see the hidden content once you press the thanks button. There's 3.28GB of stuff in this torrent but the keymaker is in there as well. I just tested on my ASA5505. There's 3.28GB of stuff in this torrent but the keymaker is in there as well.
I just tested on my ASA5505. As stated above, download Hex workshop open the.exe for the keygen.
Hit ctrl+f, for type select 'text string' then for value look for 5540. There's 3.28GB of stuff in this torrent but the keymaker is in there as well. I just tested on my ASA5505. That's the ASA version of the 'everything IOS' collection - well, IOS up to 2010 anyway. I was looking for newer versions of anyconnect.
Just adding my $0.02. The keygen has worked on every 55xx I've tried. Yes, you have to dial back your greed on the 5505. If you attempt to enable things it doesn't do, it'll complain and ignore them.
I have a tiny script that claims to be a pix license generator, but I've not actually tried it. If one of these old 506's will run long enough, I'll see what it does. Edited by seamonkey, 02 September 2013 - 06:16 AM. @ djayelusion, I have literally just now managed to get the keygen to work on my 5505. It had exactly the same software version as your 5510, and the keygen won't work with that software. I tried every variation of the keygen until concluding that. You can update to 8.2(2).
Go to post #133 in this thread where a very helpful person has posted the files you need. You can upgrade from 7.2(2) to 8.2(2) directly, but be aware that such is not always the case. Read this update guide: I did the update ten minutes ago. The keygen license was then accepted. It makes no difference whatsoever that it says 5540 on the keygen; it does not alter the key.
Thanks to everyone helpfully posting the keygen, updates and advice in this thread! Licensed features for this platform: Maximum Physical Interfaces: 8 VLANs: 20, DMZ Unrestricted Inside Hosts: Unlimited Failover: Active/Standby VPN-DES: Enabled VPN-3DES-AES: Enabled SSL VPN Peers: 25 Total VPN Peers: 25 Dual ISPs: Enabled VLAN Trunk Ports: 8 Shared License: Enabled AnyConnect for Mobile: Enabled AnyConnect for Cisco VPN Phone: Enabled AnyConnect Essentials: Enabled Advanced Endpoint Assessment: Enabled UC Phone Proxy Sessions: 24 Total UC Proxy Sessions: 24 Botnet Traffic Filter: Enabled This platform has an ASA 5505 Security Plus license. Edited by foxyrick, 27 September 2013 - 03:59 PM. @ djayelusion, I have literally just now managed to get the keygen to work on my 5505.
It had exactly the same software version as your 5510, and the keygen won't work with that software. I tried every variation of the keygen until concluding that.
You can update to 8.2(2). Go to post #133 in this thread where a very helpful person has posted the files you need. You can upgrade from 7.2(2) to 8.2(2) directly, but be aware that such is not always the case.
Easy capture usb 2.0 software. Read this update guide: I did the update ten minutes ago. The keygen license was then accepted. It makes no difference whatsoever that it says 5540 on the keygen; it does not alter the key. Thanks to everyone helpfully posting the keygen, updates and advice in this thread!
Licensed features for this platform: Maximum Physical Interfaces: 8 VLANs: 20, DMZ Unrestricted Inside Hosts: Unlimited Failover: Active/Standby VPN-DES: Enabled VPN-3DES-AES: Enabled SSL VPN Peers: 25 Total VPN Peers: 25 Dual ISPs: Enabled VLAN Trunk Ports: 8 Shared License: Enabled AnyConnect for Mobile: Enabled AnyConnect for Cisco VPN Phone: Enabled AnyConnect Essentials: Enabled Advanced Endpoint Assessment: Enabled UC Phone Proxy Sessions: 24 Total UC Proxy Sessions: 24 Botnet Traffic Filter: Enabled This platform has an ASA 5505 Security Plus license.